- Read Whatsapp Db File Online
- How To Open Whatsapp .db File In Windows
- View Whatsapp .db Files
- Read Whatsapp Db.crypt12 Files On Pc
This DBF Opener helps you to view the content of those ancient DBase database files without installing any software. After extracting the database, you can view the data with our built-in viewer or export all tables as CSV files. Upload a file: Or enter a URL: Max. File size for upload is 25 MB. Supported file types: dbf. T his tutorial shows you how to read WhatsApp messages on PC without the Crypt Key. You can read WhatsApp messages on PC for WhatsApp Database from Crypt6 to Crypt 12. Put your WhatsApp Database file you want to read right on your default SD Card; that is, where WhatsApp stores your Database file primarily.
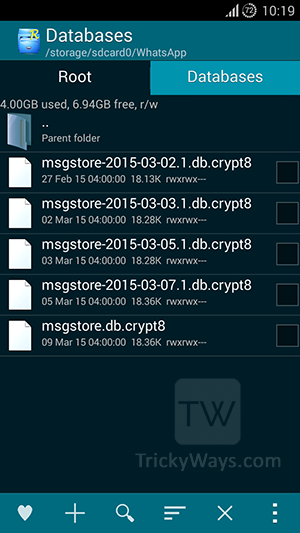
If you go to that folder, you will find a file with the name msgstore.db.crypt12 there, and several more files with names like msgstore-2016-11-08.1.db.crypt12. Msgstore.db.crypt12 is the file with the latest WhatsApp chat backup. This is the file used for automatic chat and contact recovery after reinstallation of WhatsApp.
April 27, 2014 - PRLog -- As you may know, all your WhatsApp chats messages are saved in an encrypted (*.db.crypt) file on your Android device when backing up. But how to open the WhatsApp backup Crypt file on computer? Backuptrans Android WhatsApp Transfer provides an easy way to retrieve WhatsApp Messages from Crypt file into Backuptrans local database on computer. Then you can view, export, print or transfer whatsapp messages freely. Easy to use and no technical knowledge required.Tutorial will show you how to Open WhatsApp Crypt File and retrieve Messages on computer step by step:
http://www.backuptrans.com/tutorial/decrypt-read-chats-from-whatsapp-backup-file-on-android.html
Step 0: Backup WhatsApp Conversations on Android Phone.(Skip if done)
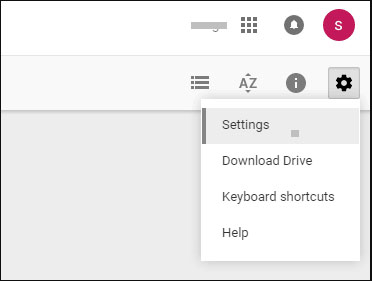
1) Go to WhatsApp > [Menu Button] > Settings > Chat Settings
2) Tap [Backup Conversations]
Step 1: Connect your Android phone to computer via USB and then copy the folder named WhatsApp from Android SD card to computer. You can find your WhatsApp backup folder on:
/storage/emulated/0/WhatsApp
or
/sdcard/WhatsApp
Step 2: Run Backuptrans Android WhatsApp Transfer software, right click database icon and then choose 'Import Android WhatsApp Backup Data'.
 Step 3: Select the WhatsApp backup database file(*.db.crypt*) on computer. Then click 'OK' to continue.
Step 3: Select the WhatsApp backup database file(*.db.crypt*) on computer. Then click 'OK' to continue.Step 4: To decrypt *.db.crypt5 file, you need to enter your Android account. Then click 'OK' to continue.
Tip: You can click 'Settings' -> 'Google' ->'Accounts' on your Android Phone to find your Android account.
Step 5: Done! All your WhatsApp Messages in Crypt file have been retrieved and saved on Backuptrans software. Now you can simply click 'Export', 'Print' or 'Restore' buton on tool bar if you want to export WhatsApp Messages to file, print WhatsApp Messages or transfer messages from database to device.
Free download
 Backuptrans Android WhatsApp Transfer on your computer to try from: http://www.backuptrans.com/android-whatsapp-transfer.html
Backuptrans Android WhatsApp Transfer on your computer to try from: http://www.backuptrans.com/android-whatsapp-transfer.html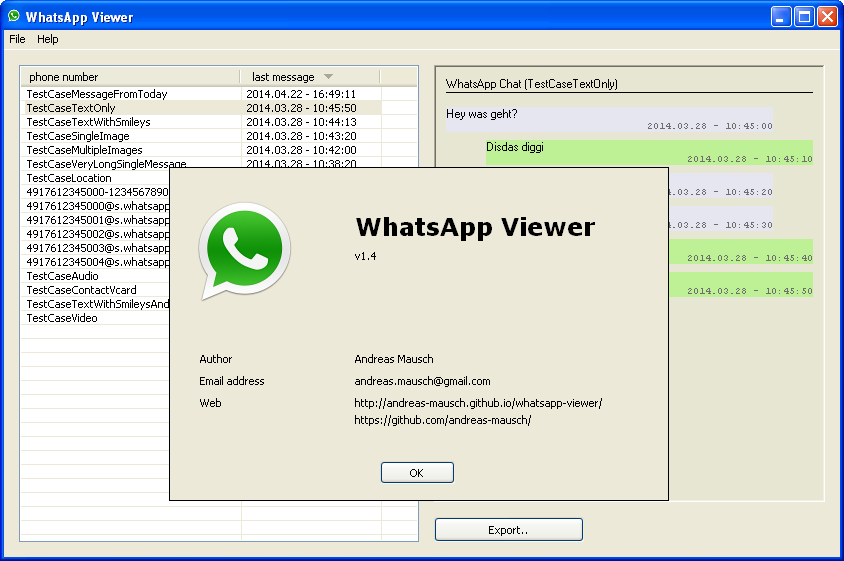
Read Whatsapp Db File Online
Best luck!How To Open Whatsapp .db File In Windows
WhatsApp backup conversation files are now saved with the .crypt12 extension. From crypt9, they seem to be using a modified version of Spongy Castle – a cryptography API library for Android.
All the findings below are based on reverse engineering work done on WhatCrypt and Omni-Crypt. I would like to highlight that IGLogger proved to be a very useful tool when it came to smali code debugging.
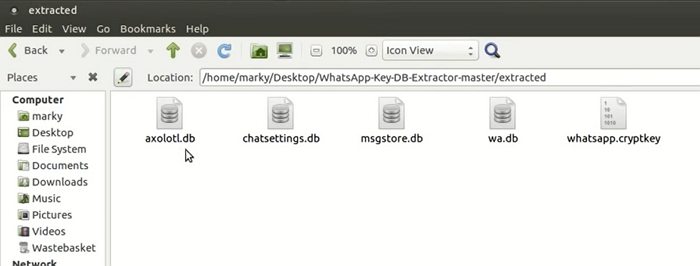
Extract Key File
To decrypt the crypt12 files, you will first need the key file. The key file stores the encryption key, K. WhatsApp stores the key file in a secure location: /data/data/com.whatsapp/files/key.
If your phone is rooted, extracting this file is easy. I will not go through the steps again, as it’s already mentioned in the crypt8 decryption article. If your phone is not rooted, refer to instructions from WhatCrypt and Omni-Crypt for details on extracting the key file. The idea is to install an older version of WhatsApp, where Android ADB backup was still working and extract the key file from the backup.
Extract crypt12 Backup File
Pull the encrypted WhatsApp messages file from your phone using ADB.
Decryption Keys
This section is just for your information and you can skip this section.
The encryption method being used is AES with a key (K) length of 256 bits and an initialisation vector (IV) size of 128 bits. The 256-bit AES key is saved from offset 0x7E till 0x9D in the file. Offsets start from 0x00. You can extract the AES key with hexdump and assign the value to variable $k.
The $k variable will hold a 64-digit hexadecimal value in ASCII that is actually 256 bits in length.
View Whatsapp .db Files
The IV or the initialisation vector is saved from offset 0x33 till 0x42 in the crypt12 file. The IV value will be different for every crypt12 file.
The K and IV extraction method is similar to what we have done for crypt8 files before.
Strip Header / Footer in crypt12 File
Read Whatsapp Db.crypt12 Files On Pc
Again, this section is just for your information and you can skip this section.
Before we start the decryption process, we will need to strip the 67 byte header and 20 byte footer from the crypt12 file.
The above dd command will strip the the first 67 bytes from the crypt12 file and save it to a file with extension crypt12.enc. The truncate command will strip the last 20 bytes from the crypt12 file.
Decrypt crypt12 File
As the WhatsApp AES cryptography API library seems to be a modified version, we will no longer be able to use openssl to decrypt the crypt12 file. I have yet to determine what has been modified.
To decrypt crypt12 files, I have written a simple Java program that will use the modified cryptography API library instead. For the cryptography API library, I have extracted the modified Spongy Castle cryptography class files from the Omni-Crypt APK file using dex2jar. You can find the Java program and crypto library over here at GitLab.
The Java program will create 3 output files:
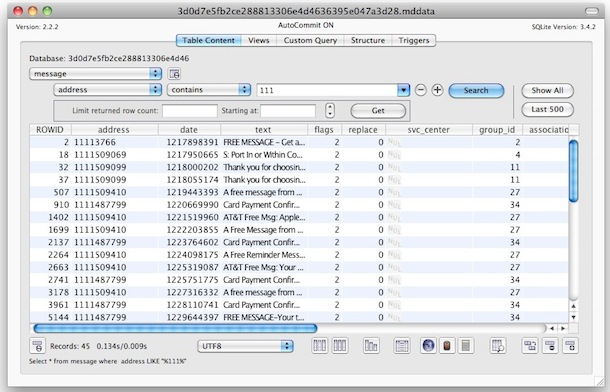
msgstore.db.crypt12.enc– encrypted file with header and footer stripped.msgstore.db.zlib– decrypted file in zlib format.msgstore.db– decrypted sqlite3 database file.
Below is how you can compile and run the Java program.
Final Words
To use the Java decryption tool, you will need to use OpenJDK. Oracle require JCE Provider libraries to be signed. OpenJDK does not have this requirement. If you try running the Java program on Oracle JDK, you will most likely get the following exception.
There are some workarounds to bypass the error, but it has not worked for me so far.
Decryption failed when using the modified cryptography API library from WhatsApp and WhatCrypt. Only Omni-Crypt library is working. I have yet to determine the reason for this. If you have any further information on this, leave a comment.
Mohamed Ibrahim
ibrahim = { interested_in(unix, linux, android, open_source, reverse_engineering); coding(c, shell, php, python, java, javascript, nodejs, react); plays_on(xbox, ps4); linux_desktop_user(true); }